Zigbee is a wireless networking protocol suitable for use in home and industrial systems.
Zigbee provides the following benefits:
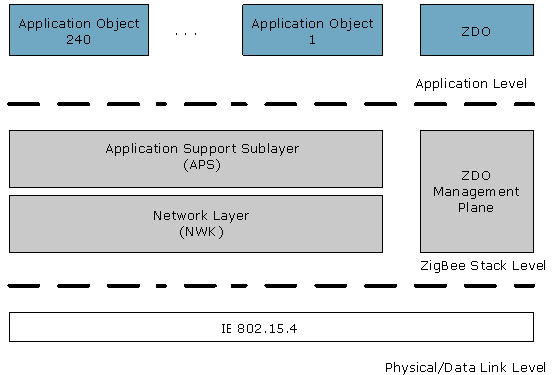
Protocol Stack
The Zigbee protocol stack consists of 3(three) layers represented in the following picture:
Communication
Frequency Bands and Channels
Zigbee communication can be established in one of the three possible radio frequency bands: 868MHz (Europe), 915 MHz (Asia and Australia) and 2400MHz (worldwide). Respectively, the bands have certain data rates concluding from the principle of "the higher the frequency, the higher the rate": 20, 40 and 250 Kbps. Each band is divided into channels. Together the three bands have 27 channels numbered from 0 to 26. To prevent from interfering with another type of radio communication, via energy detection Zigbee network management devices are capable of choosing the most suitable channel at initialization.
Transmission Range
The transmission range is between 10 to 100 m (32.8 feet - 328 feet) based on the environment. Routers can be used to extend the range of the network.
Power Consumption
The Zigbee communication rules are defined in a way to suite autonomous low-powered end devices. Such devices (security sensors, light switches, etc.) have batteries or solar cells and do not depend on power cabling. In this way, end devices can be easily installed or moved at a low cost. Some of the methods for saving power of autonomous devices is low duty cycle, sleep mode and modulation.
However, routers and coordinators must be on all the time due to their role in a Zigbee network.
Dependability
Zigbee provides reliable and secure communication. It is made reliable through the use of channel selection, "listen before sending", data encoding, message acknowledgements, and route discovery. It is secured through the use of Access Control Lists (ACL), 128-bit AES encryption and message freshness timers.
Network
Node Types
A Zigbee network can have the following types of nodes:
Topologies
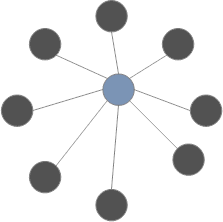
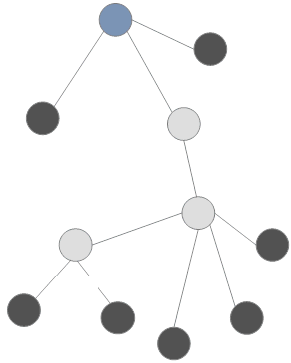
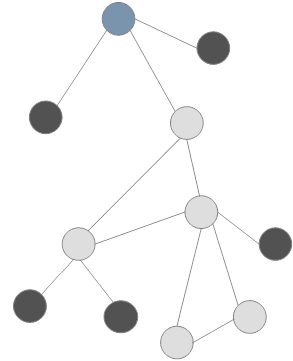
ZigBee supports the following network topologies:
![]()
Star
Contains a central coordinator node, which passes the messages to the connected end devices. The devices are within direct range to the central node. The advantages of the star configuration are that it's simple, requires no routing, and has high performance. The disadvantages are that there is no alternative if the connection between the coordinator and an end device breaks, and that the transmission range is limited.
Tree
Represents a tree-like configuration of devices whose root is a coordinator node. A tree branch starts with a router as it can have children and is capable to transmit messages down the route to a target node. The leaves can be end devices or routers whose routing feature will not be used.
Mesh
Extends the tree topology by introducing multiple routes to a certain node. Its main benefits are: "self-healing" and "self-configuring" capabilities; connections are dynamically updated and optimised; a device can be connected to several others which ensures reliability; greater network range; and easy extension and re-configuration.
Node Addressing
In a ZigBee network, nodes can be identified by one of the following address types:
Node Addressing Modes:
There may be a significant latency in propagating a message to all network nodes. This is determined by the size of the network and the number of hops the message needs to go through. If you wish to time synchronize devices you should have the node that needs synchronization periodically requesting the time from the coordinator. The coordinator then replies with a unicast message to the requesting node. In this way you minimize network traffic and can be sure that all devices are synchronized.
Software Architecture
Endpoints
A node can run several applications, and each application is represented by a node-specific endpoint. Every endpoint has an address from 1 to 240. To call an application in the network, you have to locate the device by specifying its network address or IEEE address and then the application's endpoint address. The endpoint address 255 stands for the broadcast endpoint address - by directing a message to this endpoint address the same data can be delivered to all node's applications.
ZigBee Device Objects
A special application called ZDO (ZigBee Device Objects) is accessible at endpoint address 0. It indicates the type of the node (coordinator, router or end device), initialises the node, provides join and discovery request-response capabilities, and optionally supports binding, security management, node management and group management. The ZDO Management Plane connects ZDO with the underlying APS and NWK through the rules defined in a special application profile ZigBee Device Profile (ZDP) (refer to the section below). Refer to the "Protocol Stack" section above to see the place of ZDO in the ZigBee architecture.
Device Descriptors
ZigBee nodes describe their capabilities to other entities by means of descriptors, accessible through ZDO.
The ZigBee standard defines the following types of descriptors:
Application Profiles
Application profiles represent a space of functionally related applications and devices. Usually an application profile reflects the specifics of a certain market. There are two kinds of application profiles - public and manufacturer-specific.
Several application profiles can co-exist in a ZigBee network. Moreover, a single node can support more than one profile based on the configuration of its endpoints.
Device and Service Discovery
Discovery stands for the procedure for a device to identify other devices and services in the network. Two types of discovery exist in ZigBee - device and service. A device discovery request asks for additional information about a node and is not associated with an application profile. The request can be sent to all nodes in the network by setting broadcast address 0xffff, or only to a specific node by using its network or IEEE address. A service discovery request queries for information about the services of a node - its purpose can be to determine all active endpoints of a node, get the endpoints matching specific application criteria, or get a descriptor.
Binding
Binding is a mechanism to associate a node's endpoint which produces information (source) with another node's endpoint(s) which consume(s) this information (destination). The information is communicated as clusters. For example, a switch can be bound to one or more lights. Note that to bind two endpoints successfully, they need to have compatible clusters.
Binding is decided upon by matching input and output cluster identifiers, unique within the context of a given profile and associated to an incoming or outgoing data flow in a device. Binding information is stored in binding tables, which contain source and destination pairs.
Security
Security is based on a 128-bit AES algorithm and is additional to the security model provided by IEEE 802.15.4. ZigBee security services include methods for key establishment and transport, device management, and frame protection.
The specification defines security for the MAC, NWK and APS layers. Security for applications is provided through Application Profiles.
ZigBee provides security based on three features.
Trust center
ZigBee protocol defines the role of a Trust Center - it allows or disallows new devices into its network. The Trust Center is usually the network coordinator (ZC), but it can also be a dedicated device. In a secure network the Trust Center should be only one for the rest of the devices to recognize it implicitly.
The mechanism that provides the Trust Center with its role in the Zigbee security is that it periodically updates the Network Key and switches to the new one (refer to the section below). This is done by first broadcasting the new key encrypted with the old Network Key and then messaging all devices to switch to the new key.
The Trust Center is responsible for the following security roles:
Security keys
ZigBee uses three types of keys to manage security. Security in the ZigBee network depends on the secure initialization and installation of these keys.
Master keys
Master keys are not used to encrypt frames, but are used as an initial shared secret between two devices when they perform the Key Establishment Procedure (SKKE) to generate Link Keys. They may be pre-installed during manufacturing, may be installed by a Trust Center, or may be based on userentered data. Keys that originate from the Trust Center are called Trust Center Master Keys, while all other keys are called Application Layer Master Keys.
Network keys
Network Keys perform security at the Network Layer. All devices on a ZigBee network share the same network key acquired via key-transport or pre-installation.
High Security Network Keys must always be sent encrypted over the air, while Standard Security Network Keys can be sent either encrypted or unencrypted. High Security is supported only for ZigBee PRO. Read bellow for more information on Security modes.
Although the cost of storing of Network Key is small, it reduces the system's security, because it does not prevent internal attacks (as it is shared between all network devices).
Link keys
Link Keys' role is to secure unicast messaging between two devices at the Application Layer. A device acquires link keys via key-transport, key-establishment, or pre-installation.
Keys that originate from the Trust Center are called Trust Center Link Keys, while all other keys are called Application Layer Link Keys.
Security modes
Standard
In Standard Security mode, the list of devices, master keys, link keys & network keys can be maintained by either the Trust Center or by the devices themselves. The Trust Center is still responsible for maintaining a standard network key and it maintains policies for network admittance. In this mode, the memory requirements for the Trust Center are far less than they are for High Security mode.
High
In High Security mode, the Trust Center maintains a list of devices, master keys, link keys and network keys that it needs to control and enforce the policies of network key updates and network admittance. As the number of devices in the network grows, so does the memory the Trust Center needs.